Vulnerability Assessment and Penetration Testing
Overview
The Vulnerability Assessment and Penetration Testing will be conducted to evaluate the security posture of the Network or application infrastructure based on the scope of work given to us. The objective of the assessment was to identify vulnerabilities that could potentially be exploited by malicious actors and to provide actionable recommendations to enhance the security of critical systems and data.
Key Findings
The assessment identified several vulnerabilities across the environment, categorized as follows:
High Risk: critical vulnerabilities were discovered, which could allow attackers to gain unauthorized access, escalate privileges, or disrupt services.
Medium Risk: vulnerabilities were identified that, while less severe, could still be exploited under certain conditions.
Low Risk: minor vulnerabilities were found that pose limited immediate threat but should be addressed as part of best practices.
Recommendations
To mitigate the identified risks, the following key actions are recommended:
Patch Management: Immediately apply patches and updates to all identified vulnerable software.
Strengthen Authentication: Implement stronger password policies and consider multi-factor authentication (MFA) to enhance security.
Configuration Hardening: Review and harden configurations of all critical systems according to industry best practices.
Our Methodology
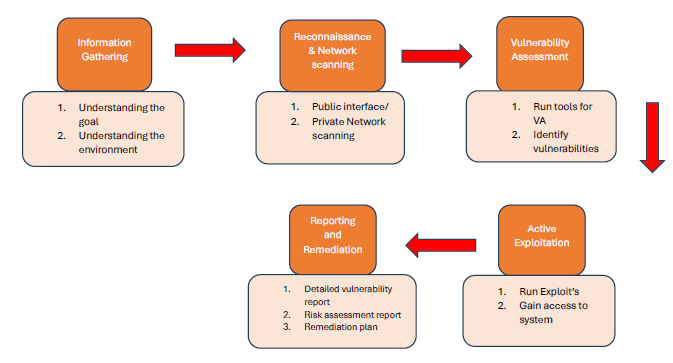
Information Gethering
- This step involves understanding the goals of the penetration test (e.g., identifying vulnerabilities, testing defenses, or ensuring compliance).We Understand the Environment and Gather information about the network's structure, including the number of devices, types of systems, and security measures based on the scope of work given.
Reconnaissance and Network Scanning
- Reconnaissance and Network scanningWe Collect information without interacting directly with the target. This may include whois lookups, DNS queries, social engineering, and searching for publicly available information.The next step is an active Reconnaissance where we directly interact with the network, such as by using tools like Nmap to scan for open ports and services.We Use tools like Nmap, Nessus, or OpenVAS to identify live hosts, open ports, services, and potential entry points.We Identify specific services running on the network, and gather details like software versions, user accounts, and configurations.
Vulnerability Assessment
- Our pen test engineer will run automated tools or manual methods to identify vulnerabilities in the network.Once the vulnerabilities are identified Analyze Findings: Prioritize vulnerabilities based on their severity, potential impact, and exploitability
Active Exploitation
- In this step we attempt to exploit identified vulnerabilities to gain unauthorized access to systems, networks, or data.If access is gained, attempt to escalate privileges to gain higher-level access.We simulate data theft and exfiltration in this step and capture the evidence.We try to maintain access in the network while being undetected.Lateral movement will be done from the compromised system.
Reporting and Remediation
- Based on the above assessment, a detailed report will be created that includes all findings, exploited vulnerabilities, methods used, and evidence gathered.Risk assessment will be done based on the potential impact of each vulnerability on the organization.Recommendations will be provided based on the identified vulnerabilities.Security measures will be implemented based on discussion with the IT Team like configuration fixes, software upgrades, OS bug fixes etc.At the end of this exercise, the engineer will be uninstallation all the tools from the target systems used during the assessment.
Pre-requisites
- List of IP addresses or internal IP ranges for assets in the NetworkAll IP addresses to be accessible from a single Laptop which can be customer provided or vendor’s machine.Provision to connect Techsiagus Network to connect the customer network via VPN or Direct access based on the consent from customer.
Deliverables
- A Penetration Testing Report containing Executive Summary, Vulnerability Details with screenshot evidence, Impact assessment, Risk Rating, and remediation plan and recommendations.
Head Office - USA
16192 COASTAL HIGHWAY LEWES, DELAWARE 19958
business@techsiagus.com
Regional office - Dubai - UAE
business@techsiagus.com
Regional office - Pakistan
business@techsiagus.com

