Security Architecture Review
Overview
A Security Architecture Review (SAR) is a systematic evaluation of an organization's IT systems, infrastructure, and processes to assess their security posture. The primary goal of the review is to identify potential vulnerabilities, risks, and weaknesses in the system's architecture and ensure that it adheres to security best practices and industry standards.:
Our Methodology
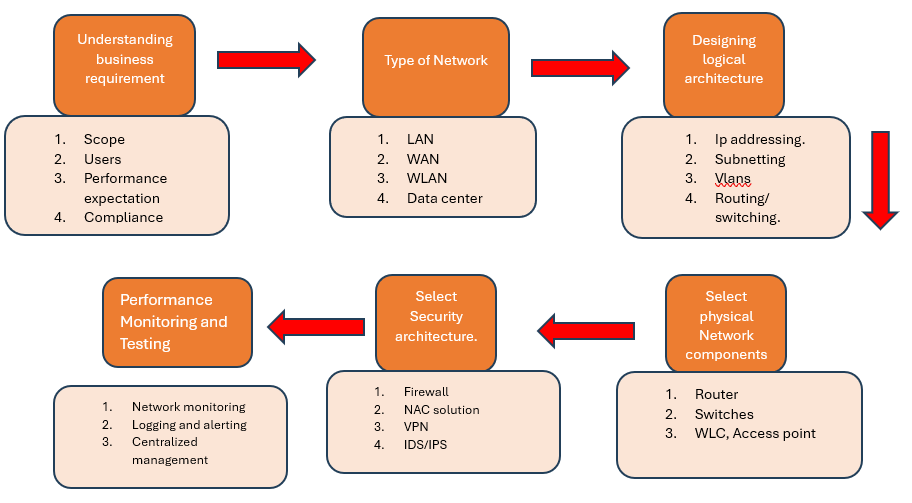
Define Security Requirements
• Understand business objectives: Align security goals with business priorities, ensuring that security enhances rather than impedes operations.
• Identify compliance requirements: Determine legal, regulatory, and industry standards (e.g., GDPR, HIPAA, PCI-DSS) that the architecture must comply with.
• Risk tolerance: Understand the organization's risk appetite to design security measures that align with acceptable risk levels.
Identify and Classify Assets
• Asset inventory: Identify all critical assets, including data, applications, networks, and hardware, to understand what needs to be protected.
• Data classification: Classify data based on sensitivity (e.g., public, internal, confidential, highly sensitive) to apply appropriate security controls.
• Business impact analysis: Assess the potential impact on business operations if these assets are compromised.
Design Security Architecture Components
• Network security: Design the network structure with segmentation, firewalls, VPNs, intrusion detection/prevention systems (IDS/IPS), and secure access points.
• Endpoint security: Implement controls for securing devices such as desktops, laptops, mobile devices, and IoT devices.
• Application security: Ensure secure coding practices, authentication mechanisms, and encryption are applied to applications.
• Identity and access management (IAM): Implement role-based access control (RBAC), single sign-on (SSO), and multi-factor authentication (MFA) to manage user access.
• Data security: Apply encryption, tokenization, and secure data storage mechanisms to protect data at rest, in transit, and in use.
Threat Modeling and Risk Assessment
• Threat modeling: Identify potential threats (e.g., unauthorized access, malware, insider threats) that could impact the system or assets.
• Assess vulnerabilities: Identify weaknesses or flaws in the design that could be exploited by attackers.
• Perform risk assessment: Evaluate the likelihood and impact of identified risks to prioritize security efforts.
Implement Security Controls
• Technical controls: Deploy technologies such as firewalls, anti-malware, intrusion detection systems, and encryption to enforce security policies.
• Administrative controls: Establish security policies, procedures, and training to ensure that users follow best practices and regulatory guidelines.
Test and Validate the Architecture
• Penetration testing: Conduct regular penetration testing to assess the effectiveness of security controls.
• Vulnerability scanning: Continuously scan the environment for vulnerabilities and ensure they are addressed.
• Security drills: Run simulations and drills (e.g., tabletop exercises) to test the incident response plan and ensure teams are prepared.
Document and Communicate Security Policies
• Security policies and standards: Document security policies, standards, and guidelines that govern how security controls are applied and maintained.
• Employee training and awareness: Provide ongoing security awareness training to ensure employees understand security policies and are aware of the latest threats.
Head Office - USA
16192 COASTAL HIGHWAY LEWES, DELAWARE 19958
business@techsiagus.com
Regional office - Dubai - UAE
business@techsiagus.com
Regional office - Pakistan
business@techsiagus.com

